Text To Binary Sucks. But You should Probably Know More About It Than …
페이지 정보

본문
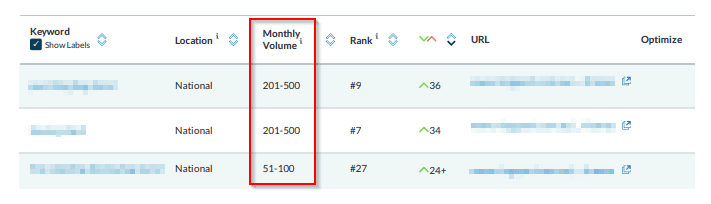
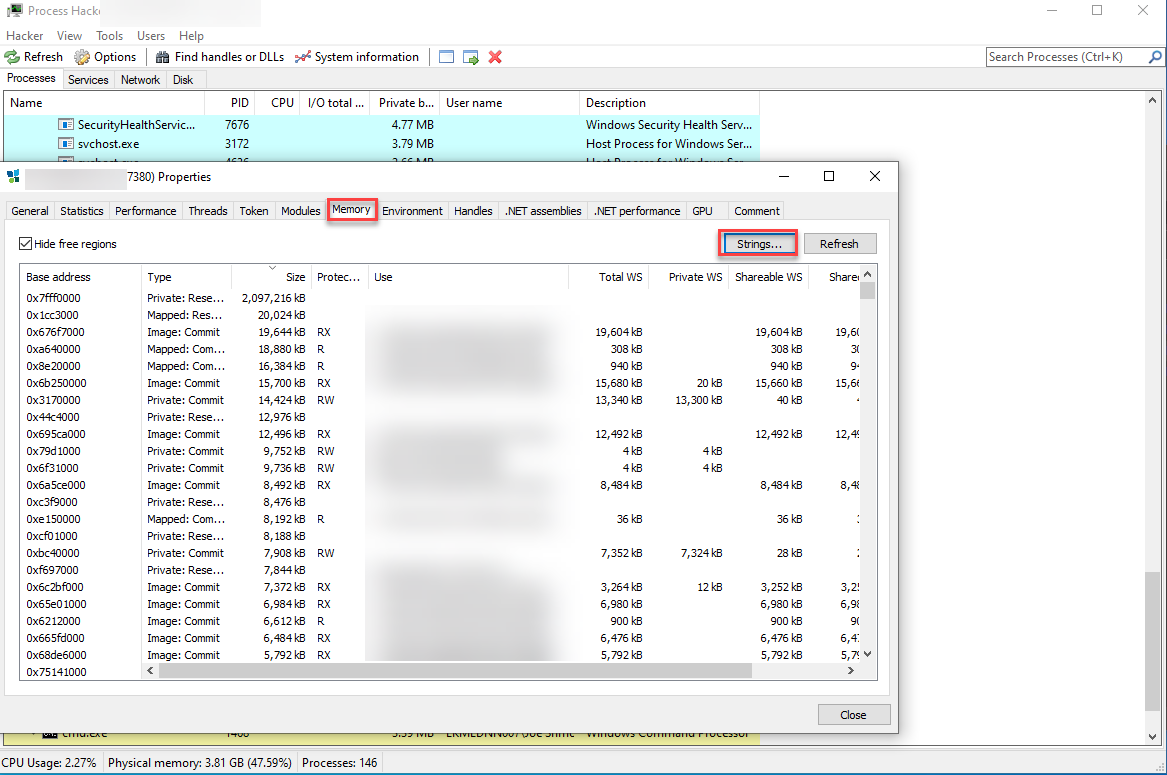 The second virtualised function was a quite simple one which immediately called exit to terminate the method. And we'll assessment that again somewhat bit in a second. Therefore, relevant key phrases with a very small search quantity (10-100) are still most likely worth focusing on if you'll be able to rank for them as each bit of traffic is effective. It can be found in the energetic reversing class. It is now in the retired part of the reversing category. The part beginning at 0x41a126 pushes an encoded string to the stack, then decodes it by XORing each byte with 0x4f. It then prints the decoded string and takes some person input through will get. Next it transforms each character of the supplied enter with a sequence of various operations, comparable to negating, xoring and left and right rotations. It takes a CRC checksum of the decrypted message to examine if the offered credential was right and try chatgpt Free prints out the message if that's the case.
The second virtualised function was a quite simple one which immediately called exit to terminate the method. And we'll assessment that again somewhat bit in a second. Therefore, relevant key phrases with a very small search quantity (10-100) are still most likely worth focusing on if you'll be able to rank for them as each bit of traffic is effective. It can be found in the energetic reversing class. It is now in the retired part of the reversing category. The part beginning at 0x41a126 pushes an encoded string to the stack, then decodes it by XORing each byte with 0x4f. It then prints the decoded string and takes some person input through will get. Next it transforms each character of the supplied enter with a sequence of various operations, comparable to negating, xoring and left and right rotations. It takes a CRC checksum of the decrypted message to examine if the offered credential was right and try chatgpt Free prints out the message if that's the case.
 You notice a bizarre sound coming out of the system, so that you throw it away in concern! The messages from the TLS callbacks make sense: we already know they perform anti-debug checks and trychatgpt. when triggered they print out some message and exit. 1 is the encoded string, param2 is the decoding key and param3 is the puts perform to print out the decoded string. When you enjoyed this writeup or solved vmcrack yourself, you might also want to take a look at the binary VM problem I wrote for HackTheBox, vvm. This binary file contains plain textual content components, again in UTF-16 little-endian, with the strings delimited by null bytes. I won’t go into depth of the ultimate virtualised perform, however my analysis can be discovered within the annotated disassembly file. The first conditional checks that the path to a bytecode file has been supplied as an argument, and if not prints an error message.
You notice a bizarre sound coming out of the system, so that you throw it away in concern! The messages from the TLS callbacks make sense: we already know they perform anti-debug checks and trychatgpt. when triggered they print out some message and exit. 1 is the encoded string, param2 is the decoding key and param3 is the puts perform to print out the decoded string. When you enjoyed this writeup or solved vmcrack yourself, you might also want to take a look at the binary VM problem I wrote for HackTheBox, vvm. This binary file contains plain textual content components, again in UTF-16 little-endian, with the strings delimited by null bytes. I won’t go into depth of the ultimate virtualised perform, however my analysis can be discovered within the annotated disassembly file. The first conditional checks that the path to a bytecode file has been supplied as an argument, and if not prints an error message.
Is saving time and reducing human error your top priority? You might want to initiate saving to your Pc to store those photographs until you decide to delete them. This script will forecast your development in Traffic Value and the growth in Traffic Value in your rivals. 2 is always a 4-byte value. As you can see it performs some extra anti-debug checks via the PEB, and exits early with return value 0 if they were triggered. The problem will be discovered on HackTheBox. You can also look vertically and promote your content material inside your vertical market. You agree not to use the Services to: Harm or threaten to harm anybody in any means; "Stalk" or otherwise harass some other particular person or entity; Impersonate any particular person or entity (together with a Right Dao agent), or falsely state or in any other case misrepresent your affiliation with any particular person or entity; Disseminate or transmit any content material that (i) violates any legislation (whether or not local, state, nationwide, or seo studio tools worldwide), (ii) infringes or violates any copyright, trademark, trade secret, patent or every other proprietary right (together with, however not limited to, utilizing third get together copyrighted supplies or trademarks without applicable permission or attribution), or (iii) includes third celebration info (whether or not protected as a commerce secret) in violation of a duty of confidentiality; Disseminate or transmit any worms, viruses or different dangerous, disruptive or destructive recordsdata, code, programs or different related technologies; or submit any material that incorporates software program viruses or some other computer code, recordsdata, programs or other comparable applied sciences designed to interrupt, destroy, or restrict the functionality of any computer software program or hardware or telecommunications equipment; Facilitate violations of those Terms of Service or the Sites’ Privacy Policies Right Dao reserves the correct to take any action it deems appropriate if it determines, in its sole and absolute discretion, that you've got engaged in any of those practices or in any other case violated these Terms of Service.
Previously, Google’s index used the desktop version of a page’s content when evaluating the relevance of a web page to a user’s question. But regardless of that, you get this idea that Google has this type of sense of how the web page performs of their search results. A larger page with more options and related material provides to the value of your page and reveals way more authority. Today I will probably be discussing a pattern binary which features virtual machine obfuscation, an obfuscation approach where the source code is compiled to a customized bytecode language and executed by an interpreter for this language. However it appeared as if it will at all times result in an error, and it was never used in the bytecode so I couldn’t examine it any additional and chose to signify it with a ud2 instruction. There were a few handlers whose objective was still unclear, such as the very last handler which appeared to test the Thread Information Block to match the stack base to the stack restrict and decrease the stack base if needed. It begins with a typical function prologue, then pushes the parameters onto the stack and backs up some registers.
If you have any sort of inquiries concerning where and the best ways to utilize free chat gpt, you could call us at our own website.
- 이전글Demisting Double Glazing Tools To Improve Your Everyday Lifethe Only Demisting Double Glazing Trick Every Person Should Know 25.02.14
- 다음글Moz Page Rank Checker - The Six Figure Problem 25.02.14
댓글목록
등록된 댓글이 없습니다.
